RaRa2World - IT Professional information highway
This blog is about IT, ITes services, cyber security, information security, training & awareness of information technology subjects. Always provide best of the market knowledge and content for enhancement of area of IT; digital. Making IT community to perform better and assisting for business enablement. Working along with IT technology we can optimize the services, cloud tech, InfoSec, Virtualization, Networking, applications are root of the IT, ITes industries. I can serve you better.
Thursday, July 16, 2020
Thursday, July 9, 2020
Wifi security for home and office network for information security
We in the world of technology, using internet through Wifi access in personal and public area.
Information security and data privacy is
big concern now for everyone because we do not know how and from where our information
may leak and misuse.
Wi-Fi become essential as all family members are using it
for internet access for multiple reasons
The active device which bridge your access and internet
cable (service provider). The router could be combine equipment with wireless
(Wi-Fi).
Router, plays a role which is managing your internet access
with security and restriction as well. Hence if there is any loophole that may
leak your data and information. Hacker may easily steal data or misuse internet
facility.
3. Placing of router, gateway in house and office
One of the biggest safety point as your router physical
location must be safe and hidden. To avoid any physical damage, hard reset and
tempering of the device, power or its cable etc.
4. Default password change
Next, most of the times it is observed that after initial
installation and configuration people do not change default password which is
very vulnerable and threat for router access by hackers.
5. Default ip-address change
OEM has typical setup and ip address for setup and easy
installation; everyone knows the default ip address because it’s part of admin
guide itself. Therefor default ip address should be changed and
6. Hide
identity of Wifi
SSID (Wi-Fi identify) is
visible name of internet to which you are connecting devices. SSID should be hidden
means it should not be broadcasting. Visible can be attacked and hidden will
not be known. Hidden SSID will make you connect Wi-Fi manually that is one pain
for first time setup, after that your device connection itself from next
connection attempt.
7. Do Not use
common name to get identify- that’s your router
Your device name should be such that it will not reveal your
identity. Like if your name is Mike Goldman so you should not keep Mike or
Goldman in router’s identity.
8. MAC address
filter and restriction
Router allow you to filter MAC address which
restrict other to get into network. It is one of the good practice for network
security and information security.
9. Strong
password
After successful configuration for the first time you should
immediately change password. Keep password strong means at least 8 to 14 length
of complex password.
10. Wifi protocol – WPA
There are three security programs which support by Wi-Fi
routers. They are WPA, WPA2 and WPA3 you can choose one out of these. Higher WPA
program is better.
11. Off device
when not in use
In general observation, people keep their router, Wi-Fi dongle
ON which may attract cyber-attack and attempt for Wi-Fi security break because
of its availability. Its meaning is when
not required or going out you should switch off Wi-Fi devices, except CCTV
cameras.
12. Disable
remote access of router
For remote troubleshooting by default router’s access from
out to inside traffic is allowed through multiple ports which is not safe hence
it must be disabled after success configuration, installation.
13. Firmware
& software update
It is recommended to keep your device upto date like router,
computer, laptop and mobile, these are client device and any vulnerability may
harm the systems.
14 .Keep firewall ON to devices, router
Firewall safety is essential nowadays because it always keep
you protected from external attacks and unwanted harmful internet traffic. Firewall
could be part of anti-virus also.
15 .Client
devices update for patches – security and critical patches
Devices like Computer, Laptop and mobile etc which are
client for Wi-Fi access should be updated regularly and specially all critical
and security patches should be applied.
16. Office
premise protection
If Wifi is controller based, then it must be MAC filtered
and integrated with DHCP for better control. Extra authentication layer like AD
integration, RADIUS server based login will make environment more security and
robust.
Rogue AP should be avoided as that become weak entry points
for data leakage and information theft.
After all these steps and learning about Wi-Fi security parameters you please check and
comment which you already knowing and have implemented.
You'll also like:
Personal Identifiable Information (PII) security
https://www.youtube.com/watch?v=G7epUTLAblk
You input, question and suggestion are welcome.
We learn
together and grow together.
Be Smart, Be Safe
Sunday, July 5, 2020
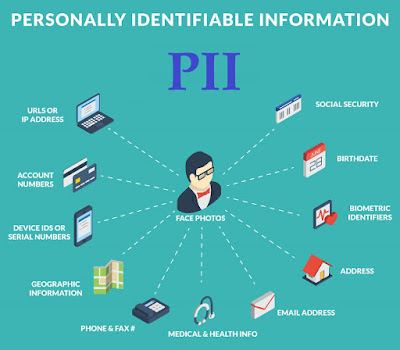
How to protect your (PII) personal identifiable information?
"We share information everywhere as we want to gather information from everywhere"
Many of us unknowingly share personal identifiable informationalso known as PII to those who are not concern with information
security or there is chance of data leakage or data theft.
Data and personal information is
critical to if break, crack and reset, unlock your secret reveal for banking,
financial and assets. Safeguard your information from hacking, information leakage. PII protection is part of information security.
What are PII, examples:
1. Name, address, SSN, date of birth, phone number, email
id
2. Financial information, location, your parents name
3. Biometric data – fingerprint, retina info
4. Medical, education, employment records
Be careful and conscious while
sharing data to agencies, consider below area where we generally share without
thinking it and we attest also, few examples are.
1. Being candidate for interview – full names with
address
2. In resume or CV also put date of birth as (mm/yyyy)
that is enough – like January 1991.
3. Opening bank account
4. Mall, petrol pump and restaurant visit for better
deal or for some prizes
5. Education class form filling
6. Online information sharing on open forum etc.
7. Sharing information for driving license, passport
number, Aadhar number, PAN number, social security number (SSN)
How to protect PII
Share information in smarter ways
- Always put purpose and recipients name while sharing (like for Citibank, for account opening, after that you only sign on document) – on every single paper.
- Always put expiry date while signing documents – valid upto 05/July/2020
- Keep date and time and purpose inside of document (not outside, at blank space), protect from to be scanned and cropped.
- Cross sign documents so signature prevail on inside area of document.
- Don’t reveal mother’s name into unwanted forms it will help hackers to crack your OTP, banking password reset etc.
- Never disclose or share CVV number for debit and credit cards.
- Limit yourself on social media with PII information.
- Don’t allow your phone to read SMS automatically, malicious apps will read OTP as well.
- Don’t share sensitive information to young children;
they may disclosure it.
Here I suggest that “Not sharing, unfolding is your PII protection; Be Smart, Be Safe.
Friday, June 26, 2020
Windows 10 2004 Release – New features
Update (May 2020): After more than a year of development, Microsoft has
started the official rollout of the Windows 10 May 2020 features update.
What’s new in Windows 10 2004, then I have
compiled a list of all the big features that you would want to know and update
machine. Many of these features were a part of various 20H1 Insider builds
and gradually these are released to public versions of Windows 10.
1. Windows 10 Cloud Download
Windows 10 2004, Microsoft brought a new feature that
makes it easier to reset your PC. This is known as Cloud Download; the feature justifies its name by downloading a
fresh copy of Windows 10 from the cloud when you need to reset the machine.
This is similar
to internet recovery feature that exists for Apple computers running through macOS.
Microsoft said
that if your internet connection is speedy, cloud restore can reset your PC
faster than the offline “imageless” recovery option. That’s because, during the
offline restore, a copy of Windows 10 is recreated from the existing
installation. It’s a time taking tasks that could take more time if the
installation has corrupt files.
2. Control Windows Update
download speeds

You might have heard people complaining about Windows
Updates sucking all of their internet bandwidth. That’s why Microsoft
introduced an option to limit the download and upload speeds for the
updates.
The newest
Windows 10 feature update brings even more download throttling options on to
the table. You can now set exactly how much bandwidth (e.g., 1Mbps, 2Mbps, and
so on) should be used for Windows Update while downloading new feature updates
and cumulative updates on your computer.
3. More data on the Network
Status page

Updates have also been made to the Network Status page in
Windows 10 2004. The revamped page now shows more information, like data usage
from various networks like WiFi, Cellular, etc.
From here,
you can directly access the properties for a particular network or check its
data usage. Earlier, this data could be viewed on the Data Usage page, which
has now been removed from the Settings app.
Also,
you’ll notice that the Airplane mode in Windows 10 is now called Flight mode.
4. Rename virtual desktops
Virtual Desktops have surely
made our lives easier by giving us more real
estate without the need for a bigger screen or a multi-monitor setup. Now in Windows 10 version 2004, you can now rename the virtual desktops as well.

5. Temperature of GPU
(graphical cpu)
If you’re looking for third-party
apps to check your GPU temperature, you can
now stop the search. Windows 10’s latest update 20H1 shows the GPU temperature,
along with other related data in the Task Manager itself. Just head over to the
Performance tab.
6. MS Paint and WordPad become
Optional
The Optional Features section in Windows
10 includes those apps and features that earlier get pre-installed on previous
Windows versions, for example, Internet Explorer.
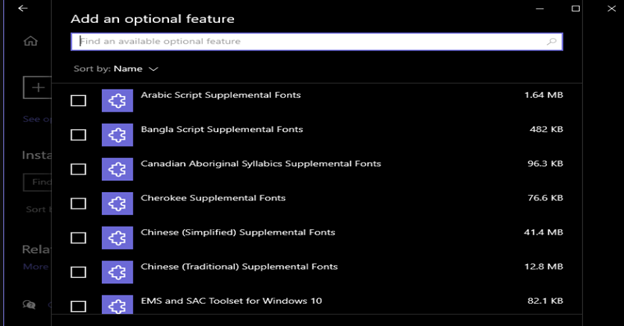
With Windows 10 version 2004, you’ll be able to select
multiple features and install all of them at the same time. As per reports, the
Paint and WordPad apps will become part of the Optional features as well.
7. Chat with Cortana
Microsoft is making another serious attempt to bring back
Cortana virtual assistant from the verge of death. Windows 10 2004 will get a
redesigned Cortana interface optimized for chat, which is currently being
tested in the US.
8. Automatic restart for
Desktop and UWP apps
There are times when you need to restart your PC, but
that also means you’ll have to reopen the apps on which you’re currently
working. Microsoft has added a new option in the 20H1 feature update that can
be of great use in such cases.
You can configure apps to restart on its own after your
PC restarts. Go to Settings. Accounts > Sign-in options. under Restart Apps,
turn on the toggle button that says, “Automatically save my restartable apps
when I sign out and restart them after I sign in.”
The app
restart works for both Win32 (Desktop apps), apps that support the automatic
restart feature. Microsoft has added manual controls so one can enable or
disable as required. Also, a similar feature available on macOS.
9. Passwordless sign-in thru
Microsoft account
Memorizing of passwords is the last thing
people want nowadays. But the in reality is, they have to do it. Unless they
put all of their trust in some good password manager.
10. File Explorer with Windows Search
The good old search bar in the File Explorer has also got its
share of features. Now, it’s powered by Windows Search, which means in addition
to local files, you can directly search for files that are stored on your
OneDrive.
If you take a closer look, you’ll realize the
visual changes that Microsoft has made to the search bar.

11. Better, faster Bluetooth devices pairing options
Windows 10
(1803) features brought better
improvements in the form of Swift Pair — a feature that allows quick pairing
with devices. Building on top of that, the new Windows 10 update will now show
one less notification during the pairing process, making it better and smoother.
Nearby
Bluetooth When a Bluetooth device is nearby and supports Swift Pair, you can
finish the pairing process right from the notification that pops up. There is
no need to open the Settings app to finish the paring process.
However,
not many people will be able to take advantage of it as the Swift Pair is
supported on a limited number of devices, with Microsoft keyboards and mouse.
Windows Subsystem for Linux (WSL) is a
great addition that lets you run various Linux distro inside Windows 10. Users
can interact with the system via the command-line interface, just like they
would on a regular Linux machine.
Tuesday, May 26, 2020
Monday, May 25, 2020
IT, digital challenges and new way of working through, by Covid19
Many IT services and their reach is changing bcoz of current
world situation
We will discuss how you can overcome and improve with some of
the areas related to IT services & its operation.
1. Team management
strategy, support measures
·
What job our team competent at.
·
Which work you can take to cloud
o Mail
services
o Essential
portals, ticketing system, reporting of servers
·
Ticketing system in place for better accountability,
work allotment
2. Communication
tools
·
In person meeting should be replaced with
Zoom/WebEx/MS Teams/Go-to-meeting etc.
·
Save on travel and avoid on public transport usage
also
·
Save on time and quicker result
3. Financial
transactions
·
Opt for online financial transaction
o NEFT, RTGS,
UPI
·
Bank to bank & bank to client
·
Digital and Contactless Payments
4. Cyber
security
·
Install perimeters, gateway, network, servers,
datacenter level protection and security appliance
·
Assessment of your devices, equipment, servers and
endpoints
·
User awareness & training on security
·
VA-PT test for critical and essentials services,
servers
·
Check compliance level for better updates and patches
·
Always need to be up to date with OS & firmware
(n-1 stable) strategy
5. On premise
and cloud
·
Determine which can on be remain onsite and which on
remote, on cloud
6. Support
·
Tools, tackle for remote support, work from home (WFH)
users
·
Enable vpn for better security, resource access
·
E-consulting will be done thru vendor, support partner
and OEM
7. Digital
transformation
·
Identify - to transform to digital work
·
Automation thru digital adoption
·
Data analytics by cloud based solution
·
Smart manufacturing adoption will take place
·
Machine condition monitoring (for OEE)
8. Hardware
·
Check your network, firewall, anti-APT, servers,
backup
·
End user computing –thin client, VDI, Cloud-VDI
·
Hyper converge system
·
Storage system
9. Software
·
Re-check if required software are available
·
Need to procure, kindly go for it
·
ERP
·
Design & Engineering software
10.
Others
·
Robotics
·
3D printing
·
Big data & analytics
·
Learning & Training
·
BCP / DR for your organization
11.
Robotics automation
·
Manual processes can be converted to RPA (robotics
process automation)
·
Save a lot of time and avoid mistakes
·
Use robots and drones to avoid touch and spread of any
infection
·
Contactless cameras and attendance system – cover 10
feet distance – remote working technology
·
3D printing for quicker and Additive, Subtractive
manufacturing
12.
Big data and analytics
·
By using data lake and data bricks huge data massaged
for output
·
Analytics help in quicker and better decisions on
output and results
13.
Learning & training
·
Helping into remote leaning
·
One session can be joined by as many
14.
Supply chain enable via
·
Industry 4.0 – real-time status from machines
·
IoT – progress update daily
·
Block chain – end to end tracking, ownership
·
Big data – huge data manageability
·
Cloud computing – On the fly deploy and compute
anything
15.
New demand
·
5G – high internet speed
·
Digitalization adoption increase
16.
IT staff capability check – competency matrix
·
Is team capable to handle task from remote
·
Is your business dependent on support partner, vendor only?
·
Consider worst scenario, check readiness
17.
DR / BCP
·
Disaster recovery – before 9/11 it was terms
·
After that Business continuity plan (BCP)
·
Better in cloud, as during city, country, world
lock-down who helped help for on premise
18.
Backup
·
Cloud should have one copy of your
·
Onsite or offsite data protection
·
Data compliance as per ISO 27001
Consider zero trust approach now.
This is applicable to all sectors companies and industries.
comment and let me know which area you have already
implemented and taken care; any area you want to take in detail please suggest.
How to become "Project Manager" | How to "Project Management" | Project Management
How to become "Project Manager" | How to "Project Management" | Project Management https://www.youtube.com/watch?v=ngLlY...

-
"We share information everywhere as we want to gather information from everywhere" Many of us unknowingly share personal ide...
-
How to become "Project Manager" | How to "Project Management" | Project Management https://www.youtube.com/watch?v=ngLlY...